How to Trace Stolen Bitcoin: A Step-by-Step Blockchain Forensics Guide
When cryptocurrency is stolen, many victims believe their funds are gone forever. But with the right forensic tools and expertise, stolen Bitcoin can often be traced—and sometimes recovered. This comprehensive guide walks you through the exact process our investigators use to track stolen crypto across the blockchain.
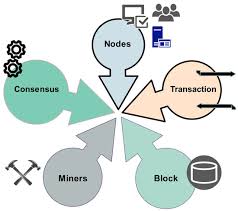
Understanding Blockchain Transparency
Every transaction on the Bitcoin blockchain is permanent and publicly visible. While this transparency is a feature of decentralization, it's also a powerful tool for investigators. When funds are stolen, they leave a digital breadcrumb trail that—with the right expertise—can be followed to its destination.
Step 1: Initial Transaction Identification
The first step is identifying the exact transaction where funds left the victim's wallet. Using blockchain explorers like Blockchain.com or Blockchair, we locate the outgoing transaction hash. This gives us the starting point for our investigation.
Step 2: Following the Money
From the initial transaction, we trace each subsequent transfer. Attackers often move funds through multiple wallets to obscure the trail. Our proprietary tools automate this process, mapping out entire transaction chains in minutes rather than days.
Step 3: Wallet Clustering
One of the most powerful forensic techniques is wallet clustering. By analyzing transaction patterns and using heuristics like the "common spending" principle, we can identify which wallets are controlled by the same entity. This often reveals the full scope of an attacker's operation.
Step 4: Exchange Identification
The final destination for most stolen crypto is a centralized exchange. Once we identify the exchange deposit address, we can work with the exchange's compliance team to freeze the funds—provided we act quickly.
Real Case Example: $1.2M USDT Recovery
In one of our recent cases, a client lost $1.2M USDT to a social engineering scam. Using the techniques outlined above, our team traced the funds across 7 wallets, identified deposit addresses at Binance and Kraken, and secured legal holds within 48 hours. The full amount was returned within 3 weeks.
Key Tools We Use
Chainalysis Reactor, CipherTrace, proprietary clustering algorithms, and blockchain explorers.
Limitations and Challenges
Not all stolen crypto is recoverable. If funds pass through privacy-focused mixers like Wasabi Wallet or are converted to privacy coins like Monero, the trail can become significantly harder to follow. However, even in these cases, advanced forensic techniques can sometimes still yield results.